Today's digital environment of cyber threats increasingly emphasizes safeguarding sensitive data as an essential business requirement at all scales, from startups to established global powerhouses. From startups with no existing identity systems to globally influential enterprises handling Personally Identifiable Information (PII), credit card details, or government ID authentications. Confidential Computing plays an essential part here by offering cutting-edge security protocols backed up with data privacy guarantees for their stakeholders' sensitive data.
Confidential Computing goes far beyond traditional data encryption methods by offering robust protection during processing - providing companies that manage sensitive information an additional line of defense where traditional approaches have failed. This revolutionary solution provides companies managing sensitive information with an effective way of securely handling their sensitive data.
Anjuna's innovative solution shines when integrated seamlessly with existing systems: creating a secure enclave - or "walled garden" for data processing free from risk or breach - within existing environments that ensure safe data processing with impenetrable defense, free from exposure or breach risks. Attestation services further solidify commitment to data security while strengthening brand trust.
Anjuna Confidential Computing Platform offers multiple uses; here are just some examples:
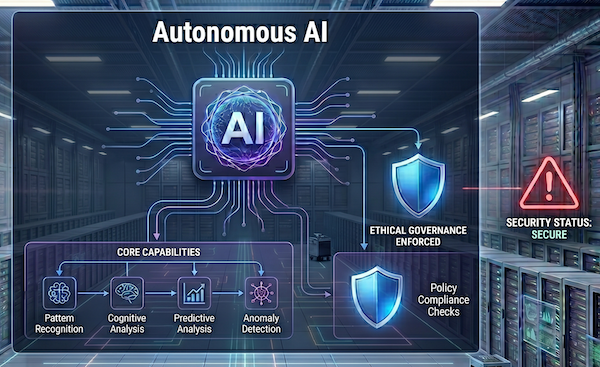
- Confidential AI: Minimize risk in data handling while training models, thwart attacks, and restrict access of collaborating parties.
- Key Management Systems (KMS): Encrypt your cryptographic keys, preventing exposure even during active processing.
- Multi-Party Computation (MPC): Enable collaborative data processing while maintaining data privacy among all parties.
- Token-based Configurations: Ensure the confidentiality of API tokens, cryptographic keys, and sensitive configurations.
- PII Protection: Implement superior security protocols for any Personally Identifiable Information operation.
Anjuna's role in revolutionizing data security is crystal clear when comparing traditional processes and the enhanced methodologies made possible through Confidential Computing.
Traditional security measures, while solid foundational safeguards, have their limitations. While practices such as encryption at rest and in transit, and boundary defenses like firewalls and network segmentation provide essential defense mechanisms against threats, continuous monitoring for compliance audits can still leave data vulnerable during processing - an issue that Anjuna technology easily addresses.
Anjuna makes data encryption an all-encompassing security measure, protecting data during processing and transmission. It creates a safe enclave to isolate processing tasks while automating policy enforcement to eliminate manual errors, integrates attestation services for demonstrable security integrity, and streamlines compliance procedures - creating an impenetrable security environment.
Confidential Computing has become an unavoidable necessity in today's digital landscape, where data serves both an economic and an ethical function. Solutions like Anjuna go above and beyond traditional security protocols to protect data at every turn - acting not simply strategically but committed to upholding unbreakable trust with your clientele while upholding data integrity at each step. Adopting Confidential Computing signals your commitment and stands as a courageous stand for data integrity. If you are ready for more, contact us or join our live demo.
Try free for 30 days on AWS, Azure or Google Cloud, and experience the power of intrinsic cloud security.
Start Free